

Your Fleet.
Your Data.
Your Systems.
Your fleet generates vast amounts of data—but is it driving better decisions?
With CalAmp Telematics Cloud (CTC), you get real-time, structured data from your vehicles, equipment and assets, delivered seamlessly to your enterprise systems. No data silos. No integration headaches. Just actionable intelligence.
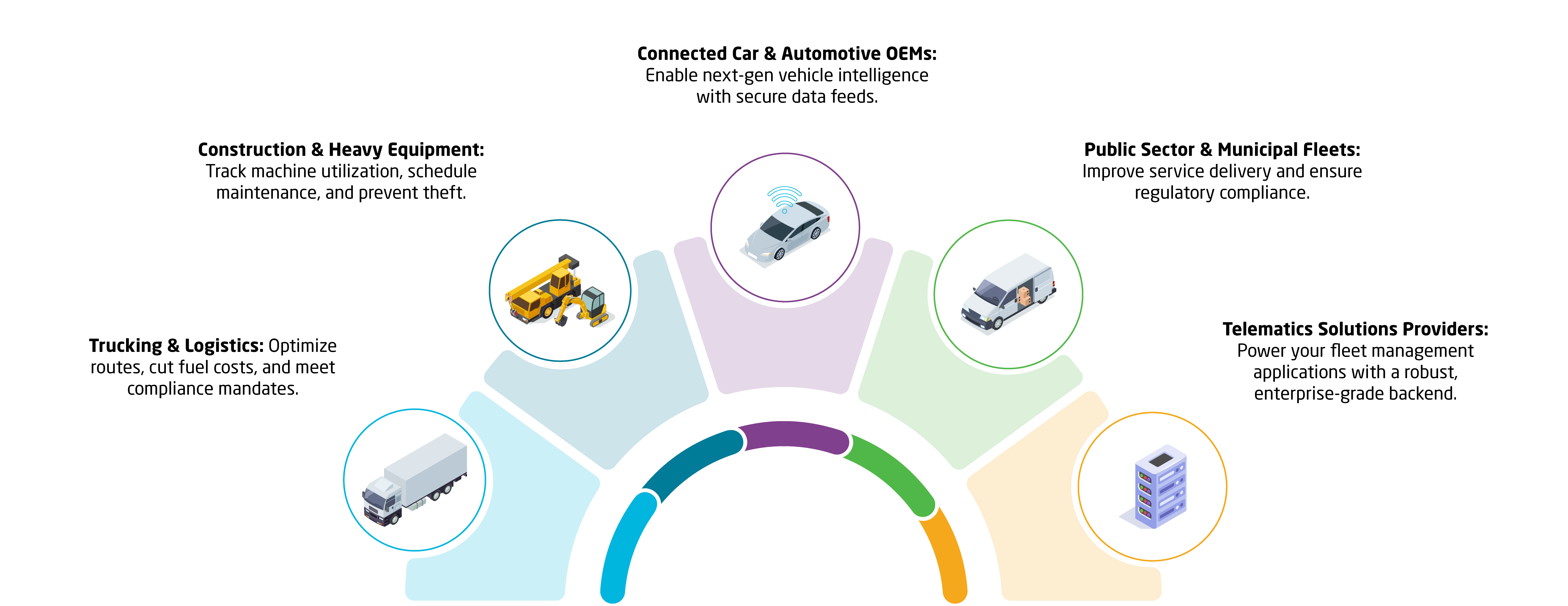
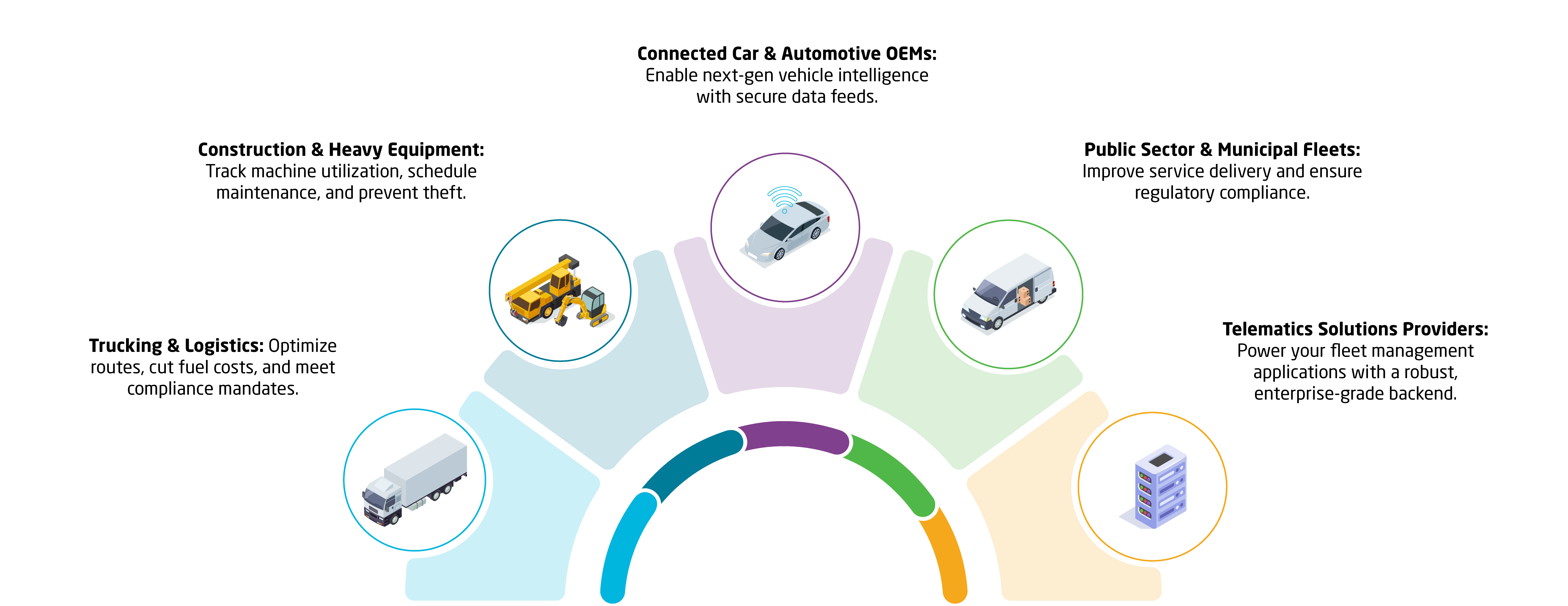
Designed for Systems Integrators, Enterprise Logistics Companies, Fleet Operators, and OEMs
CalAmp Telematics Cloud is an enterprise-grade IoT data platform (PaaS) designed for commercial fleets and software solutions providers in construction, trucking, utilities, public sector, and equipment OEMs.
It ingests, normalizes, and enriches raw telematics data from vehicles & sensors through edge devices, then delivers it directly to your enterprise IT ecosystem via a single unified pipeline.
- Works Out-of-the-Box with CalAmp’s industry-leading telematics devices
- Real-Time Data Processing for faster decision-making
- Flexible Integration Options—connect to your cloud, ERP, analytics, or proprietary systems.
- Enterprise-Grade Security & Reliability—Always protected, always on.
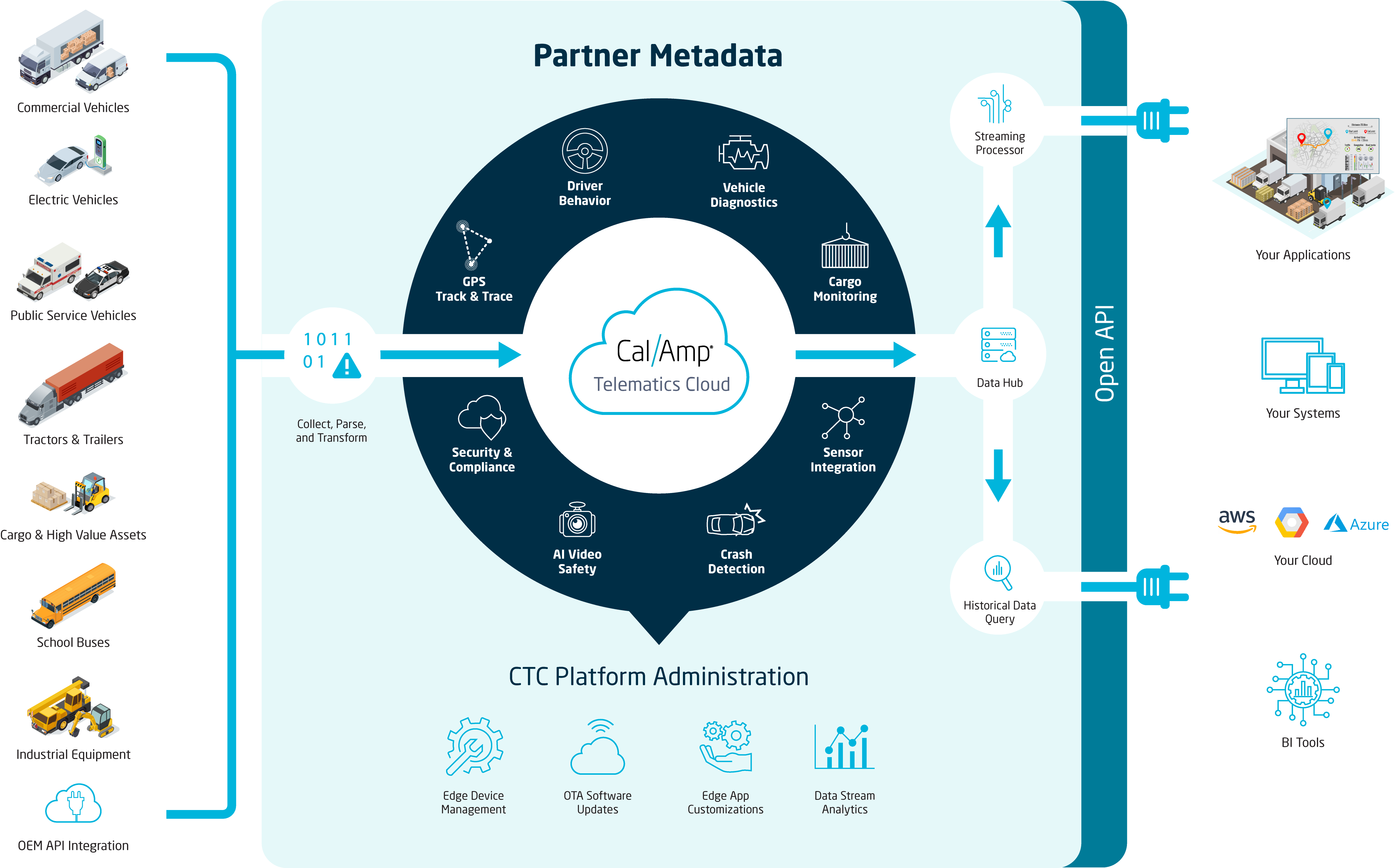
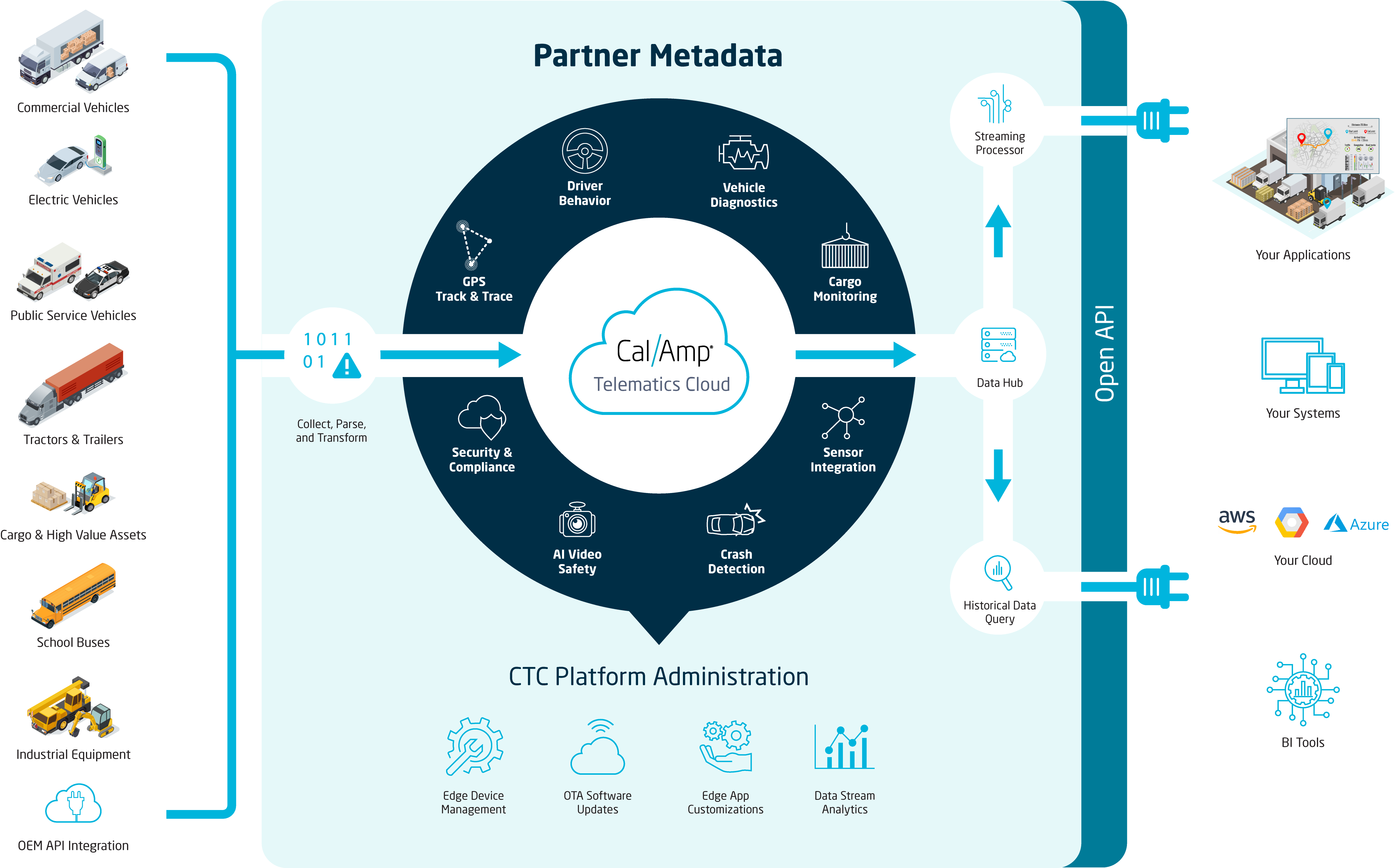
How It Works
STEP 1: Capture
CalAmp’s high-performance telematics devices, including fleet trackers, asset trackers, and vehicle gateways, collect real-time data on location, speed, engine health, driver behavior, external sensors, and more.
STEP 2: Process & Enrich
Our cloud platform applies industry-compliant decoding and enrichment to transform complex protocols like CAN bus, J1939, OBD-II, and Modbus into clean, structured, and actionable insights—ready for real-world decisions.
STEP 3: Deliver
Access your data instantly via APIs, cloud connector, or event-driven alerts. Whether you’re feeding an application, ERP, TMS, cloud storage, or analytics platform, CalAmp integrates seamlessly into your workflows to power smarter outcomes.
Built for Enterprises. Trusted by Industry Leaders.
Global assets actively managed on our platform
Availability with continuous engineering maintenance
Platform maintained 24/7 to continually ensure availability, backup and security
Fully Managed Data Pipeline
No Infrastructure Overhead
We handle connectivity, data ingestion, hosting, and security—so you can focus on your core business instead of juggling vendors or building complex IoT infrastructure.
All-in-One Gateway
One hub for vehicle, asset, and sensor data, supporting both CalAmp and third-party peripherals for easy expansion.
Hassle-Free Deployment
Devices come pre-integrated with our platform, for easy setup and quicker time-to-value with real-time insights.


Customizable Data Streams
Real-Time & Reliable
Designed for business-critical applications, our platform ensures reliable telematics data when it matters most.
Flexible Integration
REST APIs, AWS, Azure, Google Cloud, Kafka—we simplify protocol complexities.
Immediate Insights
Structured, standardized, human readable data ready for action—no cleanup required.


Scalable & Future‐Proof
Seamless Growth
Expand from 10 vehicles to 100,000+ without rearchitecting. Our auto-scaling cloud infrastructure adjusts to your evolving fleet or asset needs.
Global Connectivity, Simplified
Built-in SIM cards, automatic network switching, and carrier partnerships deliver reliable coverage—no vendor or SIM management required.
OTA Updates
Prototype on a single device and push new firmware, patches, or custom logic to thousands of devices over the air—no on-site maintenance needed.
Focus on Your Differentiators
We manage connectivity, carrier contracts, and infrastructure, allowing you to invest resources in innovation, reduced downtime, and new revenue streams.
Designed for Fleet Operators, Logistics Companies, OEMs, and System Integrators
Your Data. Your Control. Complete Security.
CalAmp Telematics Cloud is built with enterprise-grade security to protect your fleet data at every stage—from collection to cloud storage to enterprise integration.
- End-to-End Protection → Built-in encryption, role-based access, and ongoing threat monitoring.
- Regulatory Compliance → SOC 2 Type II, GDPR, SB327-compliant with secure data handling.
- Proactive Monitoring → Continuous penetration testing & security updates.
Build Custom Telematics Solutions with Ease
Explore our CalAmp Dev Portal for:
- Comprehensive API documentation
- Quick-start guides for seamless integrations
- Resources to build & scale your custom fleet solutions